
An identity-aware proxy is an access layer that sits in front of an application or service and decides whether a request should be allowed before it reaches the backend.
Instead of trusting a user because they are on the corporate network or connected through a VPN, an identity-aware proxy checks identity, evaluates policy, and grants access only to the specific resource the user is allowed to reach. In more mature implementations, it can also consider context such as group membership, IP range, device trust, location, or session conditions.
That makes identity-aware proxies an important part of modern Zero Trust access models. Rather than relying on network location as proof of trust, they move the access decision closer to the application itself.
If you only want the short version, the model is simple:
One terminology note is worth clearing up early. Identity-Aware Proxy is both a generic architectural concept and the product name Google uses for its own Identity-Aware Proxy. In this article, the term refers to the broader category.
.png)
The simplest way to understand an identity-aware proxy is to compare it with a standard reverse proxy.
A reverse proxy sits in front of an application and handles traffic on its behalf. It can terminate TLS, route requests, and present a clean public hostname. Those are useful functions, but they do not make it identity-aware on their own.
An identity-aware proxy adds access control to that front door. It does not just decide where traffic should go. It decides whether the request should be allowed before it reaches the application.
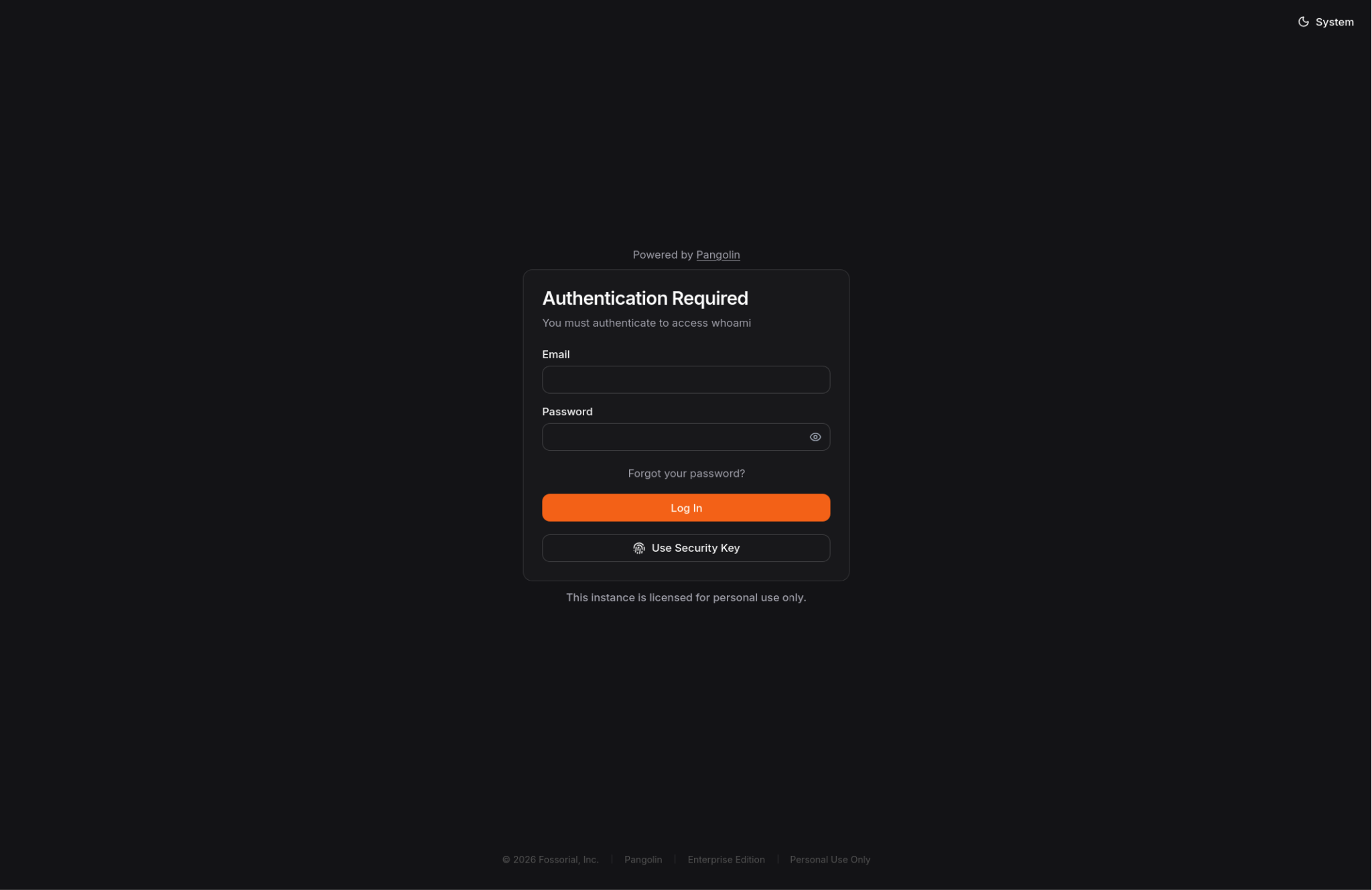
In practice, every request reaches the proxy first. The proxy checks whether the user has a valid session and, if needed, redirects them to an identity provider such as Okta, Microsoft Entra ID, Google Workspace, or Authentik. Once the user is authenticated, the proxy evaluates the request against policy.
That policy can include group membership, role, source IP, device posture, session age, geography, or reauthentication requirements.
If the request satisfies policy, the proxy forwards it to the backend. If not, the request is denied or the user is challenged for stronger authentication. Once traffic is approved, the backend receives only requests that have already passed those checks.
Many identity-aware proxies also pass trusted identity context downstream through headers such as Remote-User, Remote-Email, Remote-Name, or Remote-Role, which can help applications use identity information without building the full authentication stack themselves.
This model works best when the backend is not directly exposed and only trusts requests that come through the intended access layer.
Most organizations no longer operate inside a single, well-defined network perimeter.
Applications now span cloud platforms, on-prem environments, branch offices, and hybrid infrastructure. Employees work remotely, and contractors or partners often need access to only a small number of internal tools. In that environment, broad network access is harder to justify and harder to control.
That is where older access models begin to show their limits. A traditional VPN usually grants network-level access first and relies on downstream controls to restrict what happens next. A standard reverse proxy can publish or route traffic, but it does not automatically make access decisions based on identity and context.
An identity-aware proxy moves the access decision to the start of the request path. Instead of asking whether a user is on the right network, it asks whether this specific identity should be allowed to reach this specific application under these conditions.
This reduces unnecessary trust and makes access easier to scope. If a contractor needs one dashboard, they should not also inherit broad access to an internal subnet. If an employee needs browser-based access to an admin tool, that access should be enforced at the application front door.
These terms are related, but they are not the same thing.

In simple terms, a reverse proxy handles traffic, an identity-aware proxy handles traffic and access decisions, a VPN provides network connectivity, and ZTNA is the broader model that can include proxies, clients, and policy engines.
An identity-aware proxy is not the same as ZTNA. It is often one part of a ZTNA architecture, especially for browser-based access to internal applications, but ZTNA usually extends beyond a single enforcement point.
Another important distinction is how they operate. An identity-aware proxy is usually protocol-aware, most often for HTTP and HTTPS, while a VPN works at a lower level by routing traffic into a private network. That is why a VPN often grants broader access, while an identity-aware proxy is better suited to controlling access to a specific application or service.
When implemented well, identity-aware proxies offer several clear benefits:
Identity-aware proxies are most useful when users need access to a specific application rather than a broader network.
Common use cases include:
This model is especially effective for protecting browser-based access to private services without exposing more of the environment than necessary.
Identity-aware proxies are useful, but they are not a complete security architecture.
They do not replace application authorization, and they do not remove the need for logging, monitoring, or strong identity hygiene. They are often strongest for HTTP and browser-based access, although some platforms extend beyond that. They also depend on clear policy design and a reliable identity layer.
They are much less effective if the origin can still be reached directly and bypass the proxy. If the application remains directly exposed, the proxy becomes optional rather than authoritative. A well-designed deployment makes the proxy the real front door, not just one possible path.
If you are comparing platforms, ask a few practical questions:
The strongest solution is not the one with the longest feature list. It is the one that fits your access model and can be operated consistently.
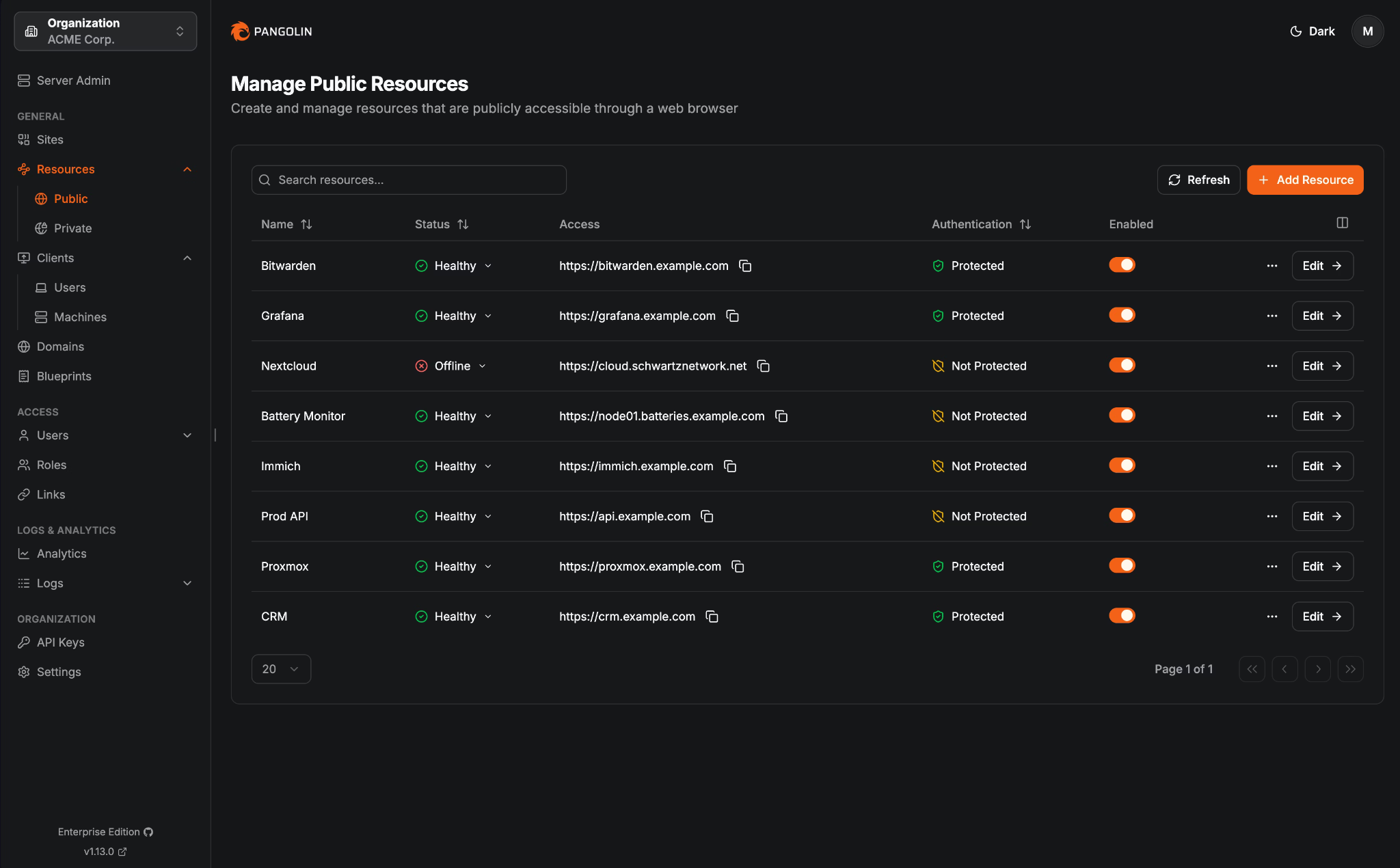
Pangolin fits this conversation well because it can implement the identity-aware proxy pattern for private web applications while also supporting broader private access models.
For browser-based access, requests hit the Pangolin server first, not the backend service directly. Pangolin evaluates identity, policy, and request context at that front door, and only approved traffic is forwarded down the tunnel to the protected resource. This creates clear separation between the access decision point and the service being protected.
That separation matters because it keeps the backend off the public internet, makes the access layer authoritative, and reduces the risk of the application being treated as directly reachable infrastructure. Instead of exposing a service and then trying to secure it in place, Pangolin keeps it behind the access layer and only carries approved traffic to it.
Pangolin is built around sites, resources, and access control. Sites connect networks back to Pangolin, while resources define the applications, hosts, or ranges users are allowed to reach. In practice, access is granted at the resource layer, while connectivity to the backend is delivered through the site hosting that resource.
That structure makes Pangolin more than a simple publishing layer. It provides an identity-aware front door for private applications while keeping the protected service behind a tunnelled access path rather than directly exposed.
For public HTTPS resources, Pangolin can sit in front of an internal web application and provide a browser-based access path without exposing the backend directly.
In practical terms, Pangolin can:
For teams looking for a cleaner way to publish and protect private applications, that maps closely to what they usually mean by an identity-aware proxy.
Pangolin is not limited to browser-based front-door access.
Its private resources support identity-based access to internal services through the Pangolin client. Access is still granted at the resource layer, but the control model differs from a standard identity-aware reverse proxy. Rather than simply placing a proxy in front of HTTP traffic, Pangolin can provide identity-based private connectivity to the systems and services a user has been allowed to reach.
This matters because many organizations do not have a single access problem. They need a consistent way to control access to internal web tools, private services, administrative paths, and hybrid infrastructure.
Pangolin is useful here because:
That makes Pangolin more than a simple identity-aware proxy. It is better understood as a private access platform that includes identity-aware proxy behaviour for web applications and extends into broader Zero Trust private access.
An identity-aware proxy is an application front door that makes access decisions based on identity and policy rather than inherited network trust.
It is a strong fit for internal web applications, partner access, contractor access, and other scenarios where broad VPN reach is unnecessary or undesirable. It also fits naturally into Zero Trust and ZTNA architectures because it moves access control closer to the resource.
For Pangolin, this is a useful entry point because it connects directly to a common buyer question: how do you protect private applications without defaulting to broad VPN access or direct exposure?
Pangolin is compelling in that conversation because it can serve as the identity-aware front door for browser-based access while also supporting broader private-resource access when the problem extends beyond a single web app.
Question: Is an identity-aware proxy the same as a reverse proxy?
No. A reverse proxy handles traffic routing and mediation. An identity-aware proxy adds authentication and policy enforcement before traffic reaches the application.
Question: Is an identity-aware proxy the same as ZTNA?
No. An identity-aware proxy is often one component inside a ZTNA architecture. ZTNA is the broader secure access model.
Question: Does an identity-aware proxy replace a VPN?
Sometimes, especially for browser-based access to internal applications. Not always. Many organizations use both patterns during migration or for different use cases.
Question: Can an identity-aware proxy protect non-web applications?
Some platforms extend beyond web apps, but the classic identity-aware proxy pattern is usually strongest for HTTP and browser-based access. Broader private access often requires a client or a different access path.
Question: Does Pangolin count as an identity-aware proxy?
For authenticated public HTTPS resources, yes. More broadly, Pangolin is a private access platform that also supports client-based private resources.